In the world of IT infrastructure, change usually happens in waves. But for embedded systems – the printers, medical devices, and industrial controllers that quietly power our world – those waves often feel more like tsunamis.
Right now, a major shift is occurring. Microsoft is aggressively pushing to deprecate NTLM (New Technology LAN Manager), the 30-year-old authentication workhorse. As Windows moves toward a “secure-by-default” posture, the fallback to NTLM is being systematically removed in favor of a modern, Kerberos-centric future.
For manufacturers and developers using embedded Linux or RTOS, this isn’t just a “Windows update” problem. It’s a connectivity crisis. If your device cannot talk Kerberos, it may soon find itself locked out of the modern enterprise network.
The Death of NTLM – the “Forgiving” Protocol
NTLM has survived for decades because it is “forgiving.” It works even when DNS is broken, when clocks are unsynchronized, or when a device only has a local IP address.
However, this flexibility comes at a massive security cost. NTLM is vulnerable to relay attacks, “pass-the-hash” exploits, and lacks mutual authentication. Microsoft’s multi-phase roadmap (already underway in 2026) aims to disable NTLM by default, forcing environments to rely on Kerberos and new extensions like Initial Authenticator Kerberos (IAKerb) and Local Key Distribution Center (KDC). The video below explains what IAKerb and Local KDC are.
Technical Challenges: Why Embedded Kerberos is Hard
Moving a resource-constrained embedded device from NTLM to Kerberos isn’t a simple toggle switch. It introduces three primary technical hurdles:
- The “Time” Problem: Kerberos is strictly time-sensitive. If your device clock drifts by more than five minutes from the KDC, authentication fails. Unlike NTLM, which is time-agnostic, Kerberos requires robust NTP (Network Time Protocol) integration to keep the embedded device in sync with the domain.
- DNS Dependency: Kerberos relies on Service Principal Names (SPNs) and DNS SRV records to locate the KDC. Embedded devices often struggle with complex DNS environments, especially in “plug-and-play” scenarios.
The Connectivity Gap: Traditionally, a client needs “line-of-sight” to the Domain Controller. In complex or remote embedded deployments, this isn’t always possible – which is why Microsoft is introducing IAKerb to allow the application server to proxy Kerberos messages.
Avoiding “Authentication Debt”
In the rush to market, many developers take a shortcut: they stick with NTLM because it’s easier to implement on a small footprint. This creates Authentication Debt.
Much like technical debt, this is a “loan” you take against your product’s future. The “interest” is the cost of emergency patches and lost contracts when your customers’ IT departments begin enforcing NTLM-off policies. By the time your device is deployed in the field for a 10-year lifecycle, that debt could become unpayable, rendering the hardware obsolete.
The YNQ Advantage: Future-Proofing Today
This is where YNQ comes in. As a high-performance SMB stack designed specifically for non-Windows platforms (Linux, VxWorks, Integrity, etc.), YNQ was built to handle the complexities of modern Windows security without the overhead of open-source alternatives.
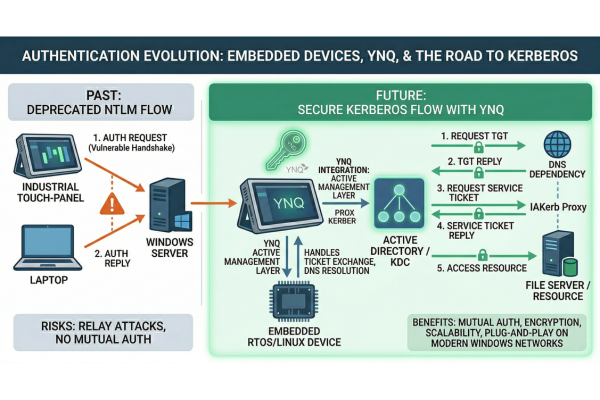
The following architecture demonstrates how YNQ replaces legacy, vulnerable NTLM handshakes with a robust, multi-stage Kerberos flow, managing the heavy lifting of ticket exchanges and DNS resolution natively within your device.
While Kerberos is still technically rooted in a shared secret (such as a machine account password or keytab), its primary advantage is that it moves the device toward a credential-less workflow on the wire. Once the initial Ticket Granting Ticket (TGT) is obtained, a process further simplified in restricted networks by IAKerb, the actual password never travels across the network again. By using YNQ to manage this encrypted ticket lifecycle, your device achieves the seamless, high-security connectivity modern enterprises demand, without the vulnerabilities of legacy password-exchange protocols like NTLM.
By integrating YNQ, your engineering team can bypass “authentication debt” and deploy a solution that is secure by default:
- Native Kerberos Support: YNQ provides built-in support for the full Kerberos lifecycle shown above, including TGT and Service Ticket requests, ensuring your device is ready for an NTLM-free enterprise.
- Small Footprint, Big Security: While Kerberos is traditionally “heavy,” YNQ is optimized for RTOS and embedded Linux, providing advanced SMBv3 security features like encryption and pre-authentication integrity with minimal RAM and CPU impact.
- Commercial Reliability: Unlike open-source projects that may lag behind Microsoft’s rapid deprecation cycles, YNQ offers a supported roadmap that keeps pace with the latest Windows Server releases.
Don’t Get Left Behind
The transition to a secure, ticket-based authentication is no longer a “roadmap item” – it is the current reality. Ensuring your embedded devices support Kerberos now is the only way to avoid the looming wall of authentication debt.
Are you ready to transition your devices to a Kerberos-based environment? Contact our experts at Visuality Systems to learn how YNQ can secure your product’s future.
Raphael Barki, Head of Marketing, Visuality Systems