SMB Protocol Explained

Integrating an SMB3 connector plugin into a Managed File Transfer solution to fulfill end-to-end encryption is a must-have requirement in certain environments.

A common challenge for IT managers and software engineers is to enable SMB protocol connectivity between Siemens’ panels and machinery servers
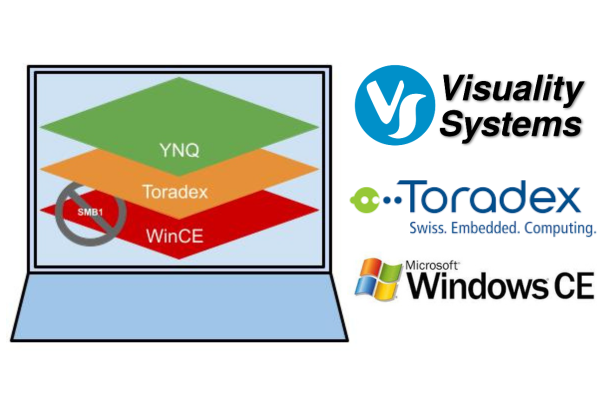
Visuality Systems and Toradex’s now offer a complete solution for Windows CE machines to overcome the drawbacks and risks associated with SMB1, without requiring extensive upgrades. Companies can now take advantage of the most cutting-edge and secure file-sharing technology, guaranteeing optimal efficiency and protection.

The QUIC protocol is becoming more and more popular among companies of all types and sizes, and is used by various applications, cloud services and IoT products, thanks to its enhanced security and overall performance. QUIC disrupts the structured TCP concept by using UDP, and by adding application level features to it.
The article talks about the decline and fall of SMB1, the reasons users should not use the protocol, and possible alternatives

SMB over QUIC Everywhere by Didier Van Hoye, Microsoft Extended Experts Team about SMB over QUIC adoption challenges

SMB over QUIC Everywhere by Didier Van Hoye, Microsoft Extended Experts Team. Visuality Systems libraries open up the market with SMB over QUIC support.
Ned Pyle, Principal Program Manager at Microsoft, introduces SMB Over QUIC, a game-changer coming to Windows, Windows Server, and Azure. QUIC offers extra security and higher performance.

VxWorks doesn’t natively support SMB. Visuality Systems’ YNQ™ — which is the only SMB for VxWorks solution — solves this problem and allows embedded systems developers to enable full SMB file sharing on any VxWorks version as well as Wind River Linux and VxWorks 653.